Cybersecurity Score
Get your Cybersecurity Score calculated
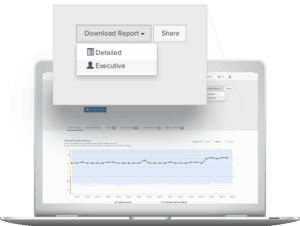
Our security score gives you an insight into your digital exposure and cyber risk. All information is purely based on publicly available information. This is the same information that is used by third parties such as CISOs, CIOs, insurers, investors, but also by cybercriminals to assess the stability of your company.
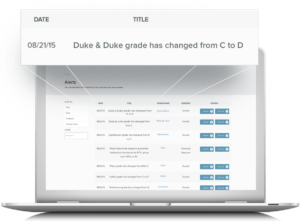
Our platform offers continuous monitoring of all your suppliers up to the 3rd and 4th degree. The cybersecurity score is divided into a wide range of risk categories such as application security, IP reputation, the patching cadence, network security and exposed passwords. Sectricity provides the security scores in subscription form or gives you direct access to the platform including remediation tips. Periodic audits and manual questionnaires are outdated solutions and are in stark contrast to this automated approach.
Avoid third party cyber-attacks
If your supplier has been hacked, it will give you indirect access to your data. It is therefore advisable to keep an eye on your ecosystem and keep the door shut for hackers.
If a supplier does not have his digital footprint under control, then all personal data can be viewed just like that.
And what about your own safety?
Do you have everything under control? Customers, investors, partners, suppliers, but also hackers can see whether your cyber hygiene is in order. For some, you may not be the right business partner, while for others, you may be a vulnerable target.
Based on this publicly available information, hackers can easily search for the vulnerabilities of your company in order to plan their cyber attack. Periodic audits or manual questionnaires are insufficient - because, by the time you receive the audit report, it is already outdated.
The security scores also work in the opposite direction, which is useful. The problem facing an audit or GRC managers is that they are able to understand and deal with their own digital exposure, but not that of their partners and suppliers. This gap can easily be filled.


Connect with our ethical hackers today!
Email: info@sectricity.com
Call: Belgium +32 9 298 05 85 or Netherlands +31 85 888 16 44
>> Free quote <<
